Why are schools cyber targets?
Just this month (April 2026), the C2k school system in Northern Ireland was targeted, disrupting A-Level revision for students across County Armagh. Days earlier, Derby High School discovered attacks that had posted staff and pupil data to the dark web.
In January 2026, Higham Lane School faced a cyber-attack that took out all digital services, including telephones, email servers and the school’s management system, forcing the school to close to students and staff for two weeks while investigations proceeded. The school’s electronic gates and fire alarm systems were rendered inoperable, meaning the safety of students could not be assured.
This wasn’t an isolated incident. New ESET research reveals that 73% of UK educational institutions experienced at least one cyber attack or breach in the past five years, with 20% reporting three or more incidents. More alarmingly, government data found that 71% of secondary schools, 86% of further education colleges and 97% of higher education institutions experienced a cyber attack in the past 12 months, compared to 50% of all UK businesses.
Schools are often seen as soft targets by cyber attackers, as the impact of any attack is felt instantly. School systems hold reams of sensitive data, and security is often the responsibility of a small IT team.
–
Why 2026 is different
According to Jisc’s annual cyber threat intelligence report, the threat landscape shows growing professionalism of cyber crime, worsened by the adoption of artificial intelligence.
The NCSC continues to respond to an increased number of ransomware attacks affecting education establishments in the UK, including schools, colleges, and universities. In recent incidents affecting the education sector, ransomware has led to the loss of student coursework, school financial records, and data relating to COVID-19 testing.
–
Hidden vulnerabilities in schools
Ransomware attackers can gain access to a victim’s network through several entry points. In recent incidents, the NCSC has observed attackers frequently target organisations’ networks through remote access systems such as remote desktop protocol (RDP) and virtual private networks (VPN). Remote Desktop Protocol remains the most common attack route used by cyber criminals to gain access to networks.
Research shows the security gaps are significant. ESET researchers found that 7% of institutions operate without an annual cybersecurity budget at all. In addition, one-third of education institutions surveyed still lack fundamental protections, such as antivirus software (33%) and strong password policies (35%). The majority (79%) have not adopted advanced measures like managed detection and response.
Jisc cyber threat intelligence saw an increase in activity where threats are targeting identity infrastructure itself, seeking ways to issue fraudulent tokens or reset credentials without user knowledge. Emerging techniques, such as deepfake audio and video impersonation, further undermine trust in traditional authentication methods.
–
What actually works?
The schools that are successfully managing cyber risk aren’t necessarily spending more money, they’re just being more strategic.
A regular review of cloud configurations and access rights is one of the simplest ways to reduce risk in 2026. Many schools choose to bring in short, targeted support via pre-approved suppliers on framework agreements, not to overhaul systems, but to sense-check settings and close obvious gaps.
For endpoint security, unpatched devices remain one of the easiest ways to hack into a network. Schools are increasingly using automated patch management systems, centralised endpoint protection, and regular vulnerability scanning.
But technical solutions alone aren’t enough. Cybersecurity is often seen as “an IT issue”, but most incidents start with human behaviour.
–
Layered security that actually works (The Dataspire Approach)
At Dataspire, we’ve developed a cybersecurity framework specifically for education that addresses both the technical and human elements of cyber resilience:
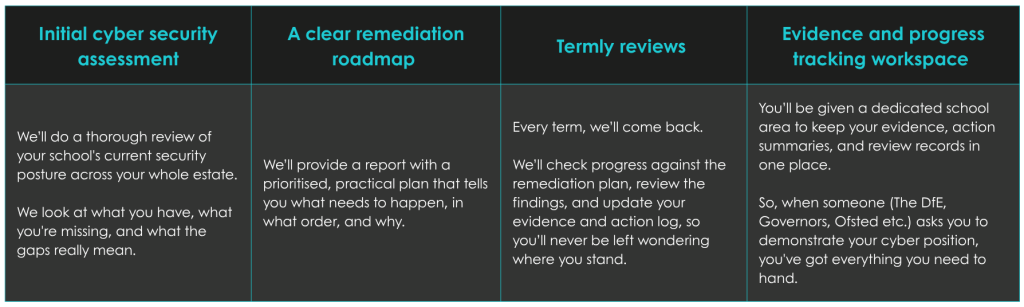
You’ll come away with a clear picture of where you’re strong, where you’re exposed, and a remediation plan that’s actually achievable within a school environment, and by achievable, we mean you’ll have a full understanding with a budget and capacity-friendly plan of action.
We work exclusively in education, so we know what realistic looks like.
–
Understanding where your school stands
Dataspire has been selected by the DfE as one of 6 suppliers to pilot cyber security standards across UK schools. That means we’re not just implementing government requirements; we’re helping to shape them by providing data that will support the DfE’s design of the 2030 Cybersecurity Standard.
That also means we’re not just familiar with what’s required. We’re actively involved in how it’s being applied in schools.
So, if you want an honest picture of your school’s cybersecurity and a clear plan to improve it, get in touch.
–
SOURCES: